How it works
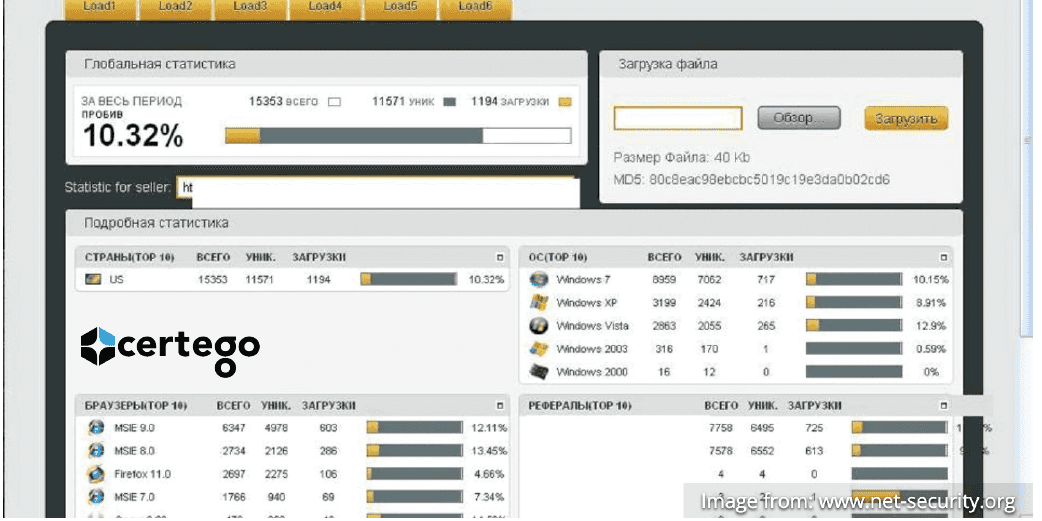
The affected forum sites have been previously compromised, possibly exploiting vulnerabilities in software platforms used for forums management, namely vBulletin version 4.1.9 and IP Board version 3.4.6. Users who visit the forum pages are redirected to external sites to download the so called Nuclear Pack Exploit Kit, a software container that provides the ability to leverage several vulnerabilities on user machines in order to infect them and gain complete control. In this particular case, files in .swf format are used to exploit the latest Adobe Flash Player vulnerabilities.
All the forums identified by Certego as being compromised during this campaign have URLs in the following format:
http://[domain]/forums/threads/[id]-[slug] with domains like:
[random_long_string].[domain] For example, these are some of the domains used to distribute Nuclear Pack, albeit not all of them are still reachable and active:
72ni9v3j9chko9ak5u4uwhf.nostaljiyemekler [.] com ey03cunzlam19kc1v9ee9jf.gumuspastabodrum [.] com ftafyk9wkvu42523ju20iri.devletdestegi [.] com We also identified some of the IP addresses on which the malicious domains are are hosted, in example:
195.154.166[.]120 213.238.168[.]139 213.238.166[.]227 Some of the IPs as well are no longer reachable and may have been cleaned, but most of them are still active and dangerous.
A few of these IP addresses belong to Virtual Private Servers purchased specifically for the installation of Nuclear Pack Exploit Kit, while others, used only as the first step in the redirection chain, are more likely to be compromised hosts. Gaining the control of these servers in the first place has allowed the creation of sub-domains with random names used for the distribution of malware. As a matter of fact, this way the Exploit Kit is reachable only by knowing beforehand the subdomain used, and is therefore much more protected from accidental discovery.
Countermeasures
This attack exploits vulnerabilities in Flash Player, which therefore must be updated to the latest version If you suspect to be already compromised, you can try to remove the infection using the following free products:
A more radical solution is to uninstall the Flash plug-in browser, or to limit the operation selectively, as explained in this guide, but this must be carefully evaluated because of the impacts it may have on usability and user experience in a production environment.